Have you faced the devastating ordeal of misplacing your copyright assets? Don't lose hope. Expert copyright recovery services are here to help you in recovering your hard-earned funds.
These skilled professionals employ the How to hire a hacker skills and advanced tools necessary to trace your case, identify the source of the loss, and maximize your chances of a successful restoration.
An reputable copyright recovery service will execute a thorough review of your circumstances, providing regular reports throughout the procedure.
By means of their unwavering efforts, they will aim to bring back your copyright assets and offer you with the peace of mind that comes from knowing that your valuable investments are secure. Don't permit this devastating event to rule your financial future.
Craving Data? Hire a Hacker - Discreet & Effective Solutions
Got an impasse? Feeling restricted by firewalls? Don't fret, we offer undetectable solutions to bypass any security. Our expert hackers can deliver the access you need, discreetly.
- We specialize in: Extracting data
- Confidentiality guaranteed:Your identity remains hidden.Your operation is our top priority.
- Results-driven:Success is our only measure.
Get in touch now for a no-obligation quote. Claim your edge with our expertise.
Need a Hacker Expert Within You?
Deepening concerns about cybersecurity threats demand immediate and specialized solutions. Searching for the right expertise can feel overwhelming, but it doesn't have to be. This Platform connects you with vetted Skilled hackers in your area who possess the knowledge to safeguard your assets. Whether you need a comprehensive security audit, penetration testing, or assistance navigating complex vulnerabilities, our network of experts is ready to provide Private guidance tailored to your specific needs. Don't wait until it's too late – Boost your defenses today with the help of a trusted cybersecurity professional.
- Benefit 1: Highlight one benefit, like “Prevent Data Breaches"
- Benefit 2: Highlight another benefit, like "Identify Vulnerabilities"
- Benefit 3: Highlight a third benefit, like "Receive Expert Guidance"
Master Hackers for Hire: Unlocking What Others Can't
In the shadowy realm of cybersecurity, where digital fortresses rise and fall with every keystroke, there exists a breed of elite hackers who operate at the pinnacle in technological prowess. These individuals, often shrouded in anonymity, possess an uncanny ability to penetrate even the most robust defenses, unveiling secrets and exploiting vulnerabilities that remain undetected from ordinary gazes.
- Seeking those with critical information needs, these cyber specialists offer their expertise as consultants, navigating the labyrinthine world of cyber warfare and extracting valuable data.
- Regardless you're facing a hostile attack or simply seeking to evaluate your own defenses, these elite hackers can provide essential insights and solutions.
Importantly it's essential to remember that the world of hacking is a double-edged sword. Engaging these specialists requires careful consideration and adherence to ethical guidelines.
Unlock Anything: Secure and Reliable Hacking Services
Looking to penetrate sensitive information? Need to audit a system for vulnerabilities? Our team of highly skilled ethical hackers provides anonymous hacking services tailored to your specific needs. We leverage the latest tools and techniques to subvert security measures without causing any harm. Whether you need to prove the strength of your defenses or gain a competitive edge, our secure and reliable services can deliver the results you desire. Contact us today for a tailored consultation and let us show you what we can accomplish.
Cybersecurity Experts: Vulnerability Audits & Simulated Attacks
Professional ethical hackers play a critical role in today's cybersecurity landscape. They perform breach assessments to expose potential weaknesses in companies' security architecture. These simulated attacks help corporations understand their vulnerability to cyber threats and implement robust mitigation strategies.
- Penetration tests typically involve reviewing a network's security controls, including firewalls, intrusion detection systems, and access policies.
- Ethical hackers also attempt to exploits to demonstrate potential vulnerabilities and propose fixes to mitigate these risks.
Consistently conducting penetration tests is vital for maintaining a robust cybersecurity posture and defending sensitive data from cyberattacks.
 Marcus Jordan Then & Now!
Marcus Jordan Then & Now! Monica Lewinsky Then & Now!
Monica Lewinsky Then & Now! Pauley Perrette Then & Now!
Pauley Perrette Then & Now!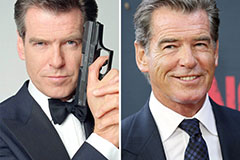 Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now! Terry Farrell Then & Now!
Terry Farrell Then & Now!